MergeLoom Docs for Ticket-to-Code Automation
Operator docs
Use these docs to get from a clean environment to your first PR or MR with validation evidence from MergeLoom ticket-to-code automation.
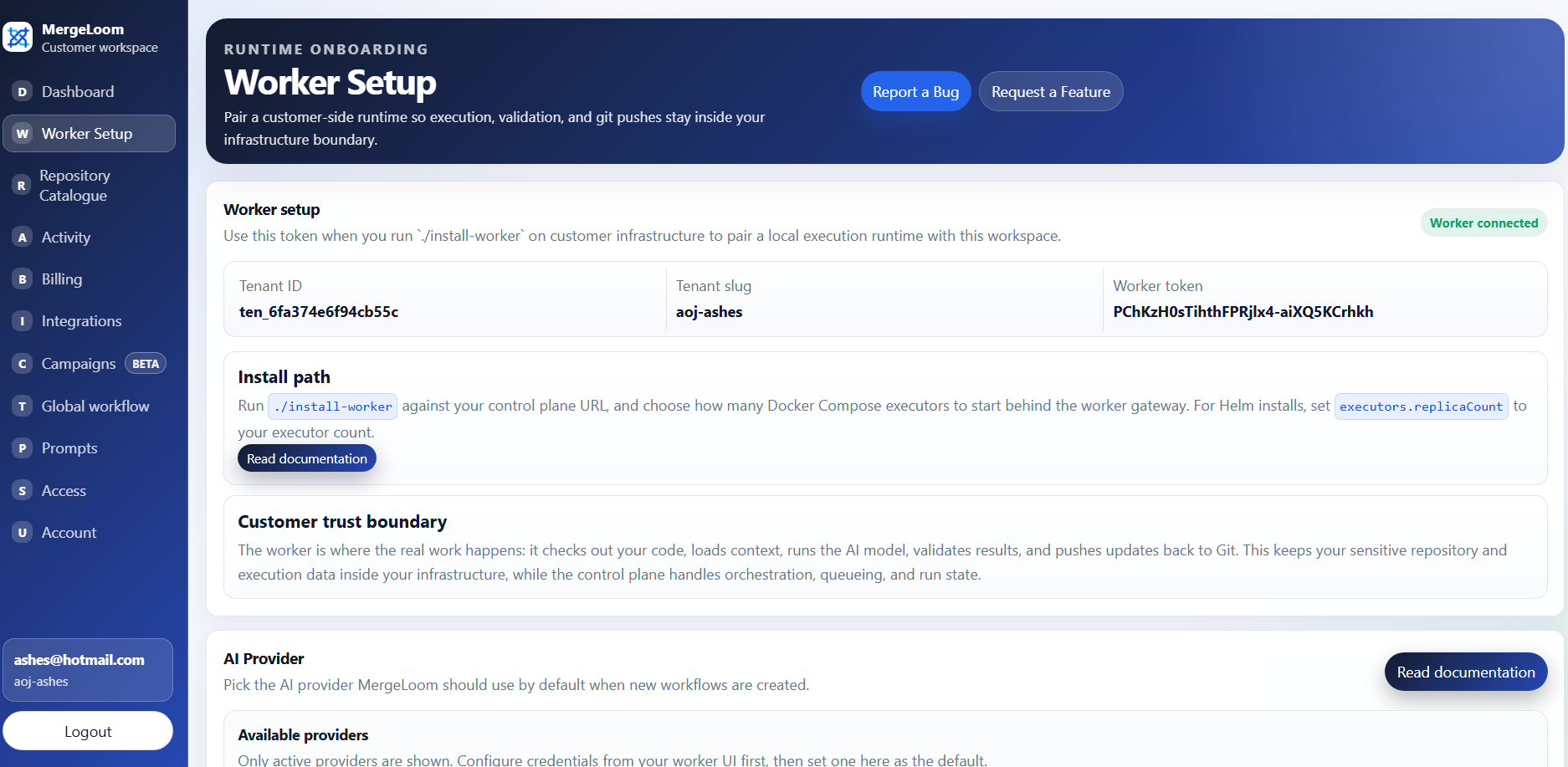
Use the MergeLoom controller at https://controller.mergeloom.ai to create
your account, connect integrations, copy worker enrollment values, configure
workflow rules, and watch runs.
Know which UI you are using
The customer controller is at https://controller.mergeloom.ai.
Use it for accounts, integrations, worker enrollment, workflow rules,
repository settings, and job audit state. The local worker UI is available
only after you install the worker, usually at http://127.0.0.1:8010/
or through an SSH tunnel to that port. Use it for provider setup, provider
readiness, local run streams, and worker-local traces.
The fastest route is:
- Install the worker.
- Configure an AI provider.
- Connect your work tracker and code host.
- Configure intake labels and workflow states.
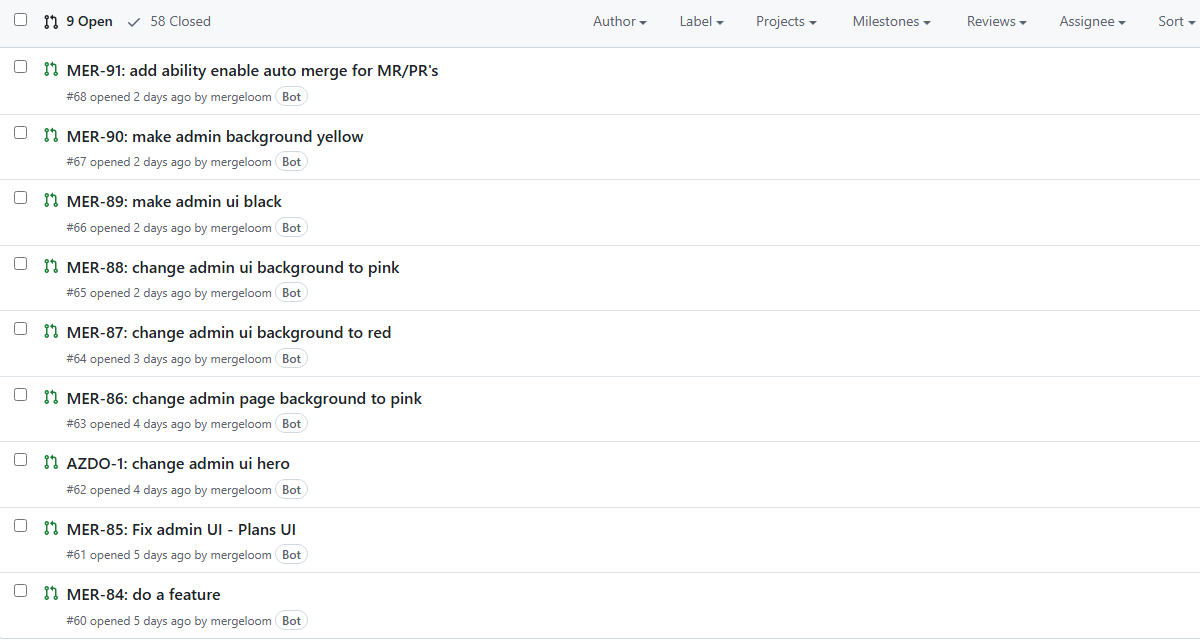
- Add the label to a ticket and watch MergeLoom create the review request.
Start here
Section titled “Start here”- What is MergeLoom?
- Quickstart
- Install the worker
- Configure an AI provider
- Connect integrations
- Configure workflow intake
- Run your first job
What these docs cover
Section titled “What these docs cover”These docs are written for engineering leads, platform engineers, and workspace admins who need to prove MergeLoom safely in a real workflow.
They focus on the current product shape:
- customer-hosted worker execution
- Docker Compose first-run path
- Kubernetes worker deployment with Helm
- worker-local provider setup
- Jira, GitHub Issues, GitLab Issues, monday.dev, Linear, and Azure Boards intake
- GitHub, GitLab, and Azure Repos review output
- labels, comments, and workflow state changes
- repository rules, validation commands, and review controls
Public installer sources
Section titled “Public installer sources”The public worker install sources are available here:
- Docker Compose installer: MergeLoom/mergeloom-worker-install
- Helm chart source: MergeLoom/mergeloom-worker-helm-chart
- Worker image:
mergeloom/mergeloom:1.0
For production Kubernetes installs, the Helm chart supports
secret.existingSecretName so enrollment tokens and provider API keys can come
from your cluster secret workflow instead of Helm values.
